Critical Infrastructure
Essential Protection
A42 – a platform that automatically monitors your company's external perimeter – domains, subdomains, exposed services, detects data leaks and vulnerabilities before they can be exploited by attackers
The playbooks of elite defenders, automated by AI agents. Built from frontline mil and gov cyber-defense experience — refined and systematized into an AI product by our team. Each scheme runs autonomously, step by step.
Trust, but verify. Even the most skilled staff and highly paid specialists are not immune to human error. Our service acts as a control mechanism - while a mistake for a specialist may result in dismissal, for you it could mean reputational damage, financial loss, or even legal liability.
Simplify your DevOps workflow. Our service can save dozens of hours of manual work, allowing your team to focus on what truly matters.
Consistency is key. We conduct scheduled scans of all your subdomains to detect vulnerabilities and errors, delivering instant reports – all without the need for manual intervention from your team.
Discovery of all subdomains, including shadow assets
We scan all your assets — automatically, bi-weekly.
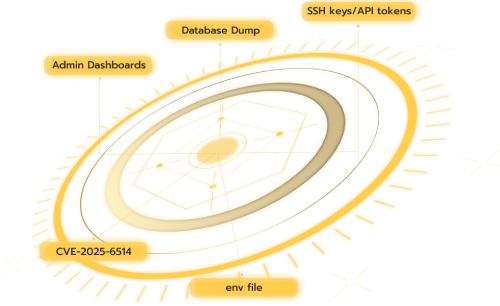
We detect exploitable vulnerabilities — not just alerts
We leverage multiple techniques and tools to accurately map all related subdomains. Our integrated approach combines broad data collection, advanced detection tools and AI algorithms.
Our product performs scheduled, recursive scans to deliver thorough exposure reports, eliminating the need for manual input and ensuring continuous monitoring.
Our system scans dark web sources for leaked credentials and sensitive data linked to your domain that may have been shared to illicit databases.
A visual tool that identifies and categorizes detected vulnerabilities, facilitating effective planning of your patch management and remediation processes.
A tool that conducts large-scale scans of your business's IP address to assess its detectability and identify potential vulnerabilities.
Get a comprehensive security assessment and protect your digital assets with our advanced cybersecurity solutions.
No complicated setup, just connect and go
Securely verify your digital assets
Get real-time alerts and recommendations
Receive a list of services in exchange for your email and the domain you want to test for your first free security assessment. If no vulnerabilities are found, you will receive a "Verified by A42" certificate. If critical vulnerabilities are identified, we will provide you with a detailed report.