The Domain Name System (DNS) is often called the "phonebook of the internet" because it translates human-friendly domain names into IP addresses, enabling seamless communication between users and websites. However, this critical system is also a prime target for cybercriminals. Attackers exploit DNS vulnerabilities for phishing, data exfiltration, malware command-and-control (C2) communications, and large-scale Distributed Denial-of-Service (DDoS) attacks. Despite its importance, many organizations overlook DNS security, relying on outdated configurations that expose them to significant risks.
To build a robust defense, it is essential to understand how attackers exploit different layers of DNS. This article explores three primary attack surfaces—Authoritative DNS, Recursive DNS, and Endpoint/User-Level DNS—along with real-world examples and strategies for mitigating threats.
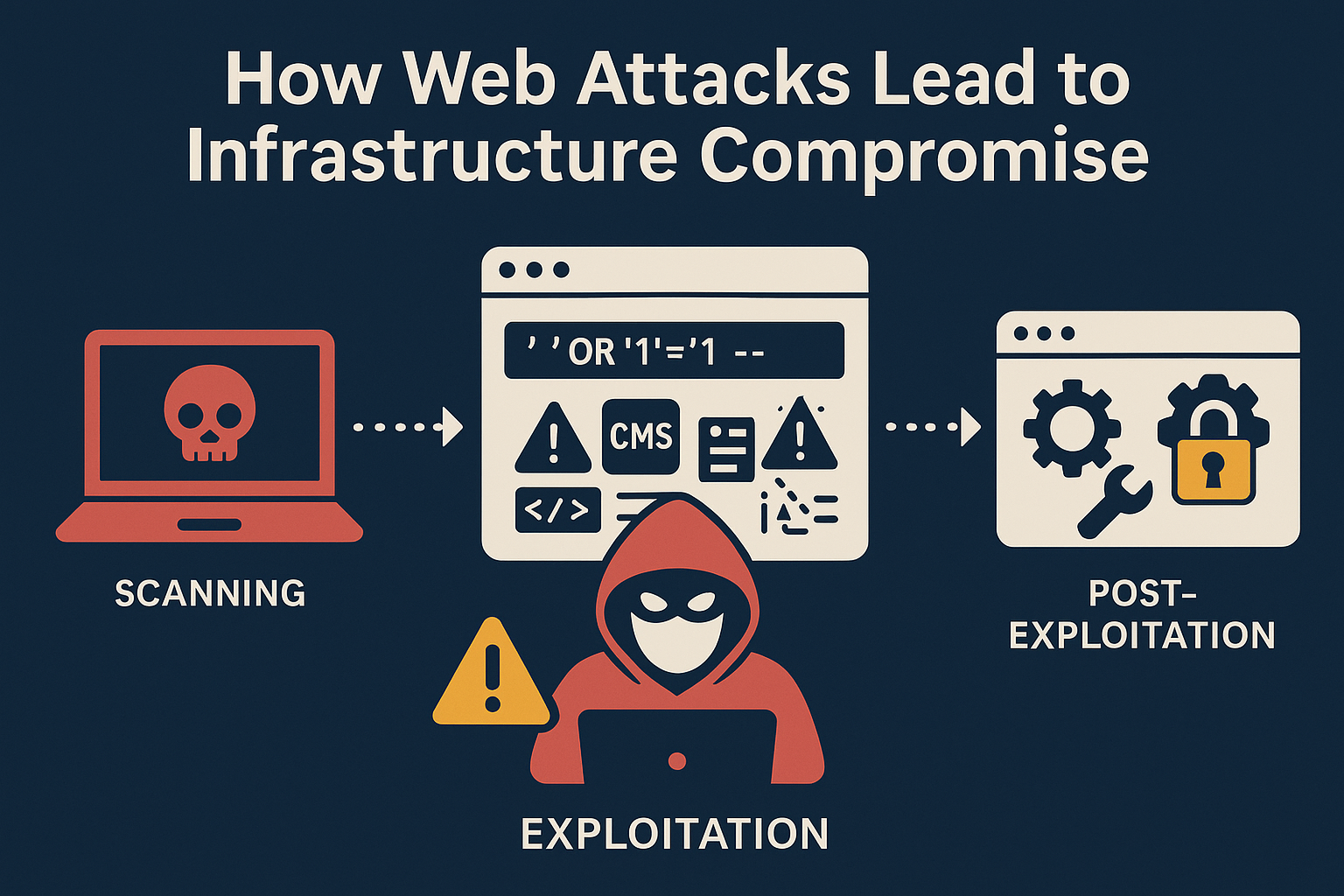
How Attackers Exploit DNS
DNS operates in a hierarchical and distributed manner, which presents multiple attack vectors. Below are the three primary layers of DNS where attackers operate, along with real-world examples and defensive strategies.
1. Authoritative DNS
Authoritative DNS servers are responsible for mapping domain names to IP addresses. If these servers are compromised, attackers can manipulate DNS records, reroute traffic to malicious websites, steal login credentials, or disrupt entire online services. Organizations that fail to protect their authoritative DNS infrastructure risk severe financial and reputational damage.
Attack Scenarios in Authoritative DNS Exploitation:
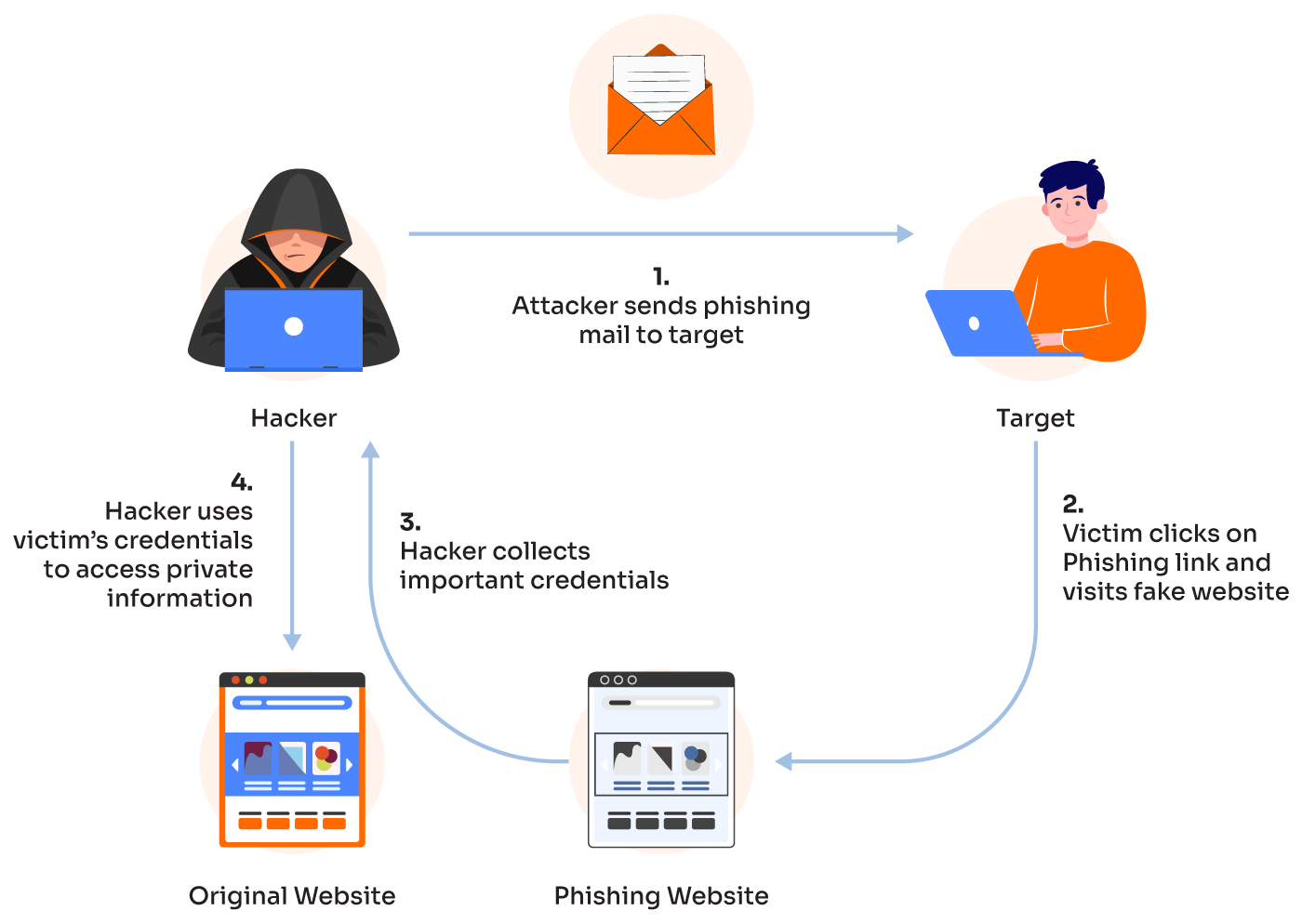
DNS Record Modification: Attackers may alter the DNS records of a target domain to redirect users to fake websites that look identical to the legitimate ones, a tactic often used in phishing attacks. For example, they may change the A (address) record of example.com to point to a malicious IP address, leading users to a fraudulent website designed to steal personal information.
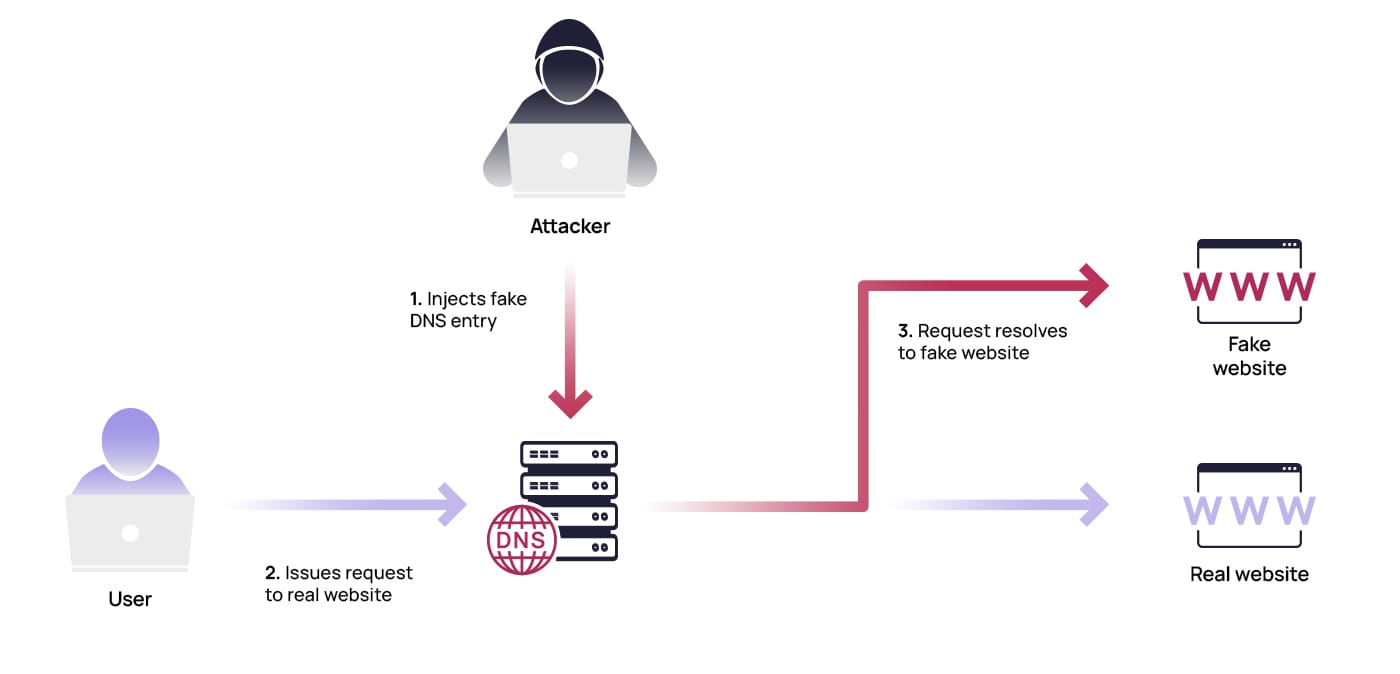
DNS Cache Poisoning: In this type of attack, an attacker can inject false DNS records into the cache of a DNS resolver, causing it to return a fake IP address to users. This can lead to the redirection of users to malicious sites, often without the user realizing it.
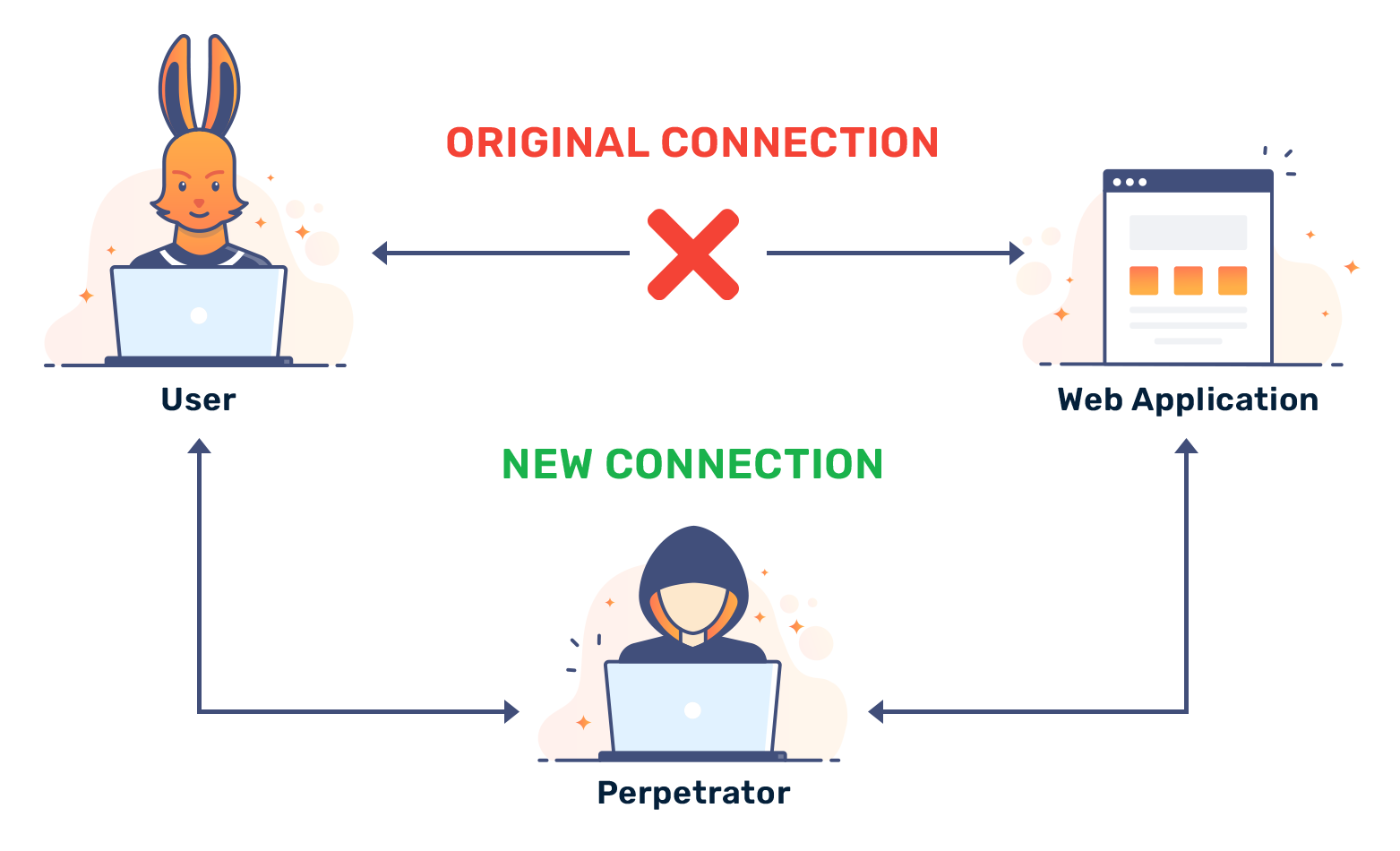
Man-in-the-Middle (MITM) Attacks: If an attacker intercepts and alters DNS queries or responses between a client and the DNS server, they can direct users to malicious sites or intercept sensitive information, such as login credentials.
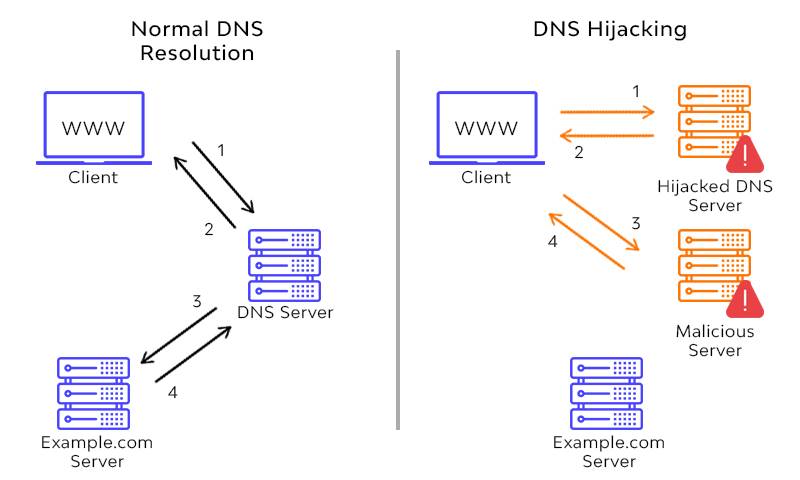
DNS Hijacking: This attack involves taking control of a domain's DNS settings, allowing attackers to reroute all traffic to malicious servers. Attackers may also modify the domain's WHOIS record to change ownership, making recovery difficult.
Denial-of-Service (DoS) Attacks: Attackers can overwhelm authoritative DNS servers with massive amounts of traffic, making the domain unavailable for legitimate users, thus affecting the availability of the targeted website or service.
Real-World Incidents:
Sitting Ducks Attack (2024): On July 31, 2024, security researchers from Infoblox and Eclypsium uncovered a large-scale DNS hijacking campaign named Ducks Now Sitting (DNS) or Sitting Ducks. Attackers managed to compromise over 35,000 domains without accessing the accounts of their legitimate owners. This method put more than a million domains at risk daily.
Sea Turtle Campaign (2019): Nation-state attackers compromised multiple authoritative DNS providers to redirect government and telecom traffic to credential-stealing sites.
How to Defend:
Implement DNSSEC: DNS Security Extensions (DNSSEC) digitally sign DNS records, preventing unauthorized modifications.
Restrict Access: Use multi-factor authentication (MFA) and strict role-based access controls (RBAC) for DNS management.
Monitor DNS Logs: Continuously inspect DNS queries for anomalies, unauthorized record changes, and potential hijacks.
Conduct Regular Audits: Identify and remove outdated or unused DNS records, especially CNAME and TXT records that could be hijacked.
2. Recursive DNS
Recursive DNS resolvers act as intermediaries between end users and authoritative DNS servers. When a user types a domain name into their browser, the recursive resolver is responsible for finding the corresponding IP address by querying multiple DNS servers if necessary. This process ensures efficient domain resolution while caching responses to improve speed and reduce the load on upstream servers.
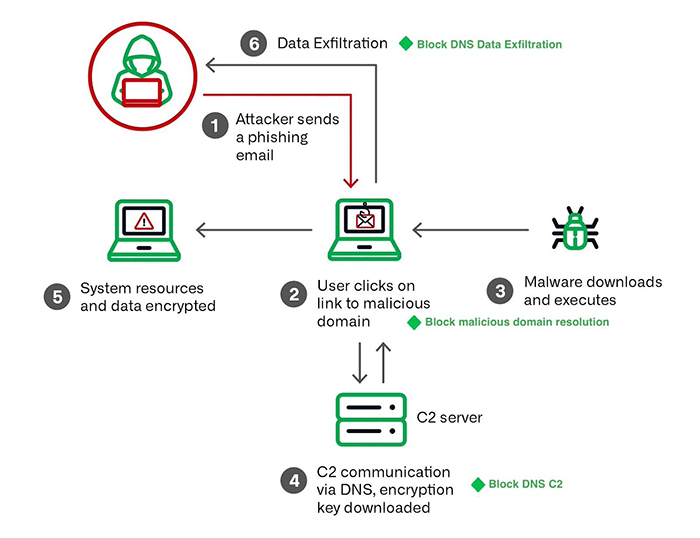
Attackers exploit these resolvers for various malicious purposes, including data exfiltration, malware distribution, and DDoS attacks.
Attack Scenarios in Recursive DNS Exploitation:
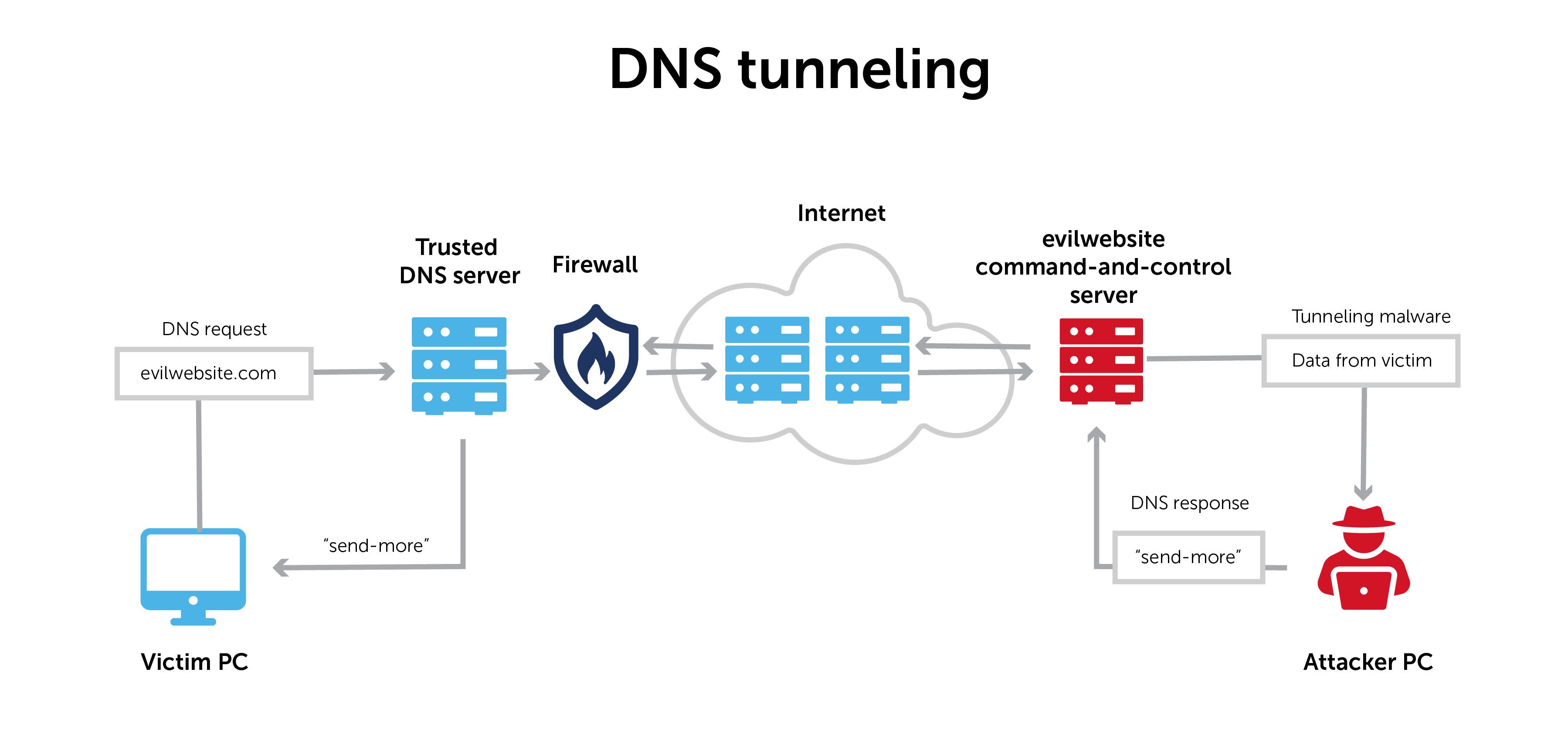
DNS Tunneling: Malicious DNS queries are used to exfiltrate data or establish covert communication channels, bypassing network restrictions.
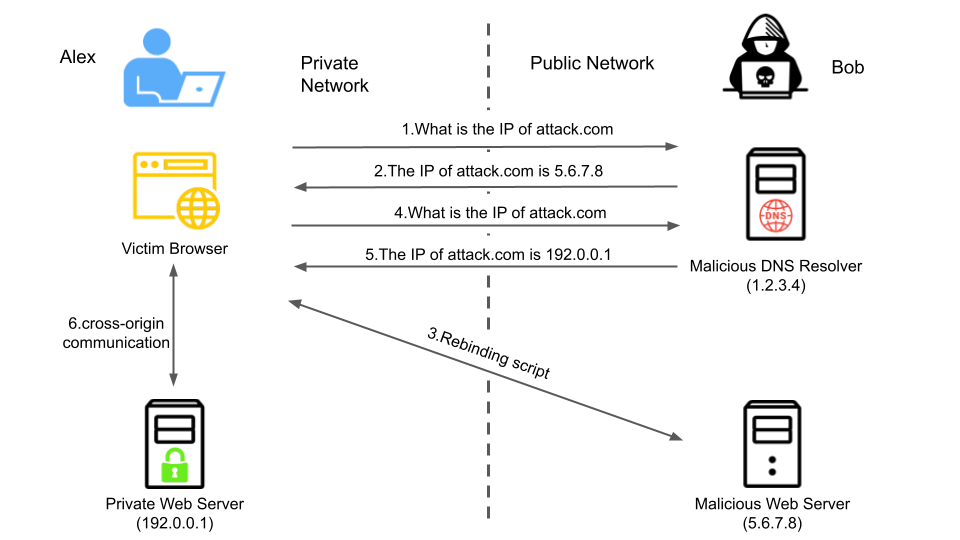
DNS Rebinding: Manipulating DNS responses to gain access to internal network resources or bypass browser security policies.
Exploitation of Open Recursive DNS Servers: Misconfigured servers are used by attackers for amplification or other attacks.
Real-World Incidents:
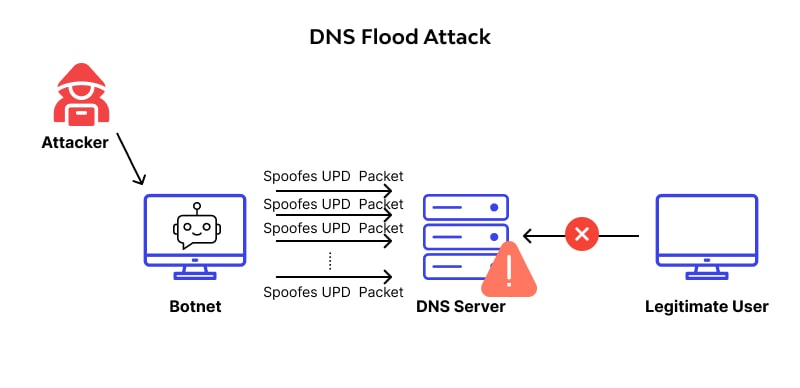
Massive DNS Flood Attacks (2024): Throughout 2024, clients of NGENIX experienced frequent DNS Flood attacks designed to overwhelm DNS servers. One such DDoS attack generated up to 6 million queries per second over two minutes, significantly impacting DNS availability.
DNS Tunneling Attacks: Threat actors encode data within DNS queries to evade firewalls and exfiltrate sensitive information. Malware such as Dnscat2 and Iodine are commonly used for this.
Command-and-Control (C2) Communication: Malware families like TrickBot and QakBot use DNS queries to locate and communicate with their C2 servers, allowing attackers to maintain persistence.
DNS Amplification DDoS Attacks (2024): In 2024, DNS amplification made up 9% of all DDoS attacks, where attackers spoof DNS requests to flood victims with massive amounts of traffic.
How to Defend:
Enable DNS Filtering: Block known malicious domains and suspicious DNS requests to prevent malware communication.
Use Rate Limiting: Apply Response Rate Limiting (RRL) on resolvers to prevent abuse in amplification attacks.
Deploy Passive DNS Monitoring: Track DNS query patterns for anomalies, such as unusually high request volumes to unknown domains.
Restrict Open Resolvers: Ensure your DNS resolvers do not accept recursive queries from external networks unless explicitly required.
3. Endpoint and User-Level DNS Security
Ensuring DNS security at the endpoint and user level is crucial for preventing cyber threats, enforcing policies, and maintaining network integrity. Since attackers often exploit DNS for malware distribution, phishing, and data exfiltration, organizations must implement robust security measures at both the endpoint and user levels.
Common Attacks:
DNS Hijacking: Attackers manipulate DNS settings on endpoints (e.g., changing the DNS server to a malicious one). This redirects users to fake websites, often for phishing or malware distribution.
Phishing via Malicious Domains: Attackers register domains that resemble legitimate ones (e.g., "amaz0n.com") to trick users into entering sensitive information on fake websites.
Malware Distribution via DNS: Malware often uses DNS to communicate with C2 (command and control) servers, exfiltrate data, or download malicious payloads.
DNS Spoofing: Attackers can provide false DNS responses to user devices, leading them to malicious sites or intercepting sensitive data.
Man-in-the-Middle (MITM) Attacks: In unsecured networks, attackers can intercept DNS traffic between the endpoint and DNS servers, manipulating responses or redirecting traffic to malicious sites.
Real-World Incidents:
DDoS Attack on Minecraft Servers (2024): In August 2024, Global Secure Layer recorded a powerful DDoS attack on unofficial Minecraft servers, reaching a peak of 3.15 billion packets per second, with a traffic volume of 849 Gbps. The attack lasted just over an hour.
DNS Hijacking via Malware: The Adrozek malware (2020) infected thousands of Windows machines, altering DNS settings to redirect users to fraudulent ad-injected sites.
Fake Domains for Phishing: Attackers register lookalike domains such as g00gle.com or paypa1.com to trick users into revealing their credentials.
Man-in-the-Middle (MitM) DNS Attacks: Public Wi-Fi networks are commonly used to intercept and alter DNS queries, redirecting users to fake login pages.
How to Defend:
Use DNS over HTTPS (DoH) or DNS over TLS (DoT): Encrypting DNS queries prevents MitM attacks and DNS interception.
Monitor Endpoint DNS Changes: Unexpected modifications in local DNS settings should trigger alerts.
Deploy Endpoint Protection Solutions: Advanced security solutions can detect and block malicious DNS traffic at the device level.
Train Employees: Educate users on phishing risks and encourage them to verify URLs before entering credentials.
Final Thoughts
DNS remains one of the most overlooked yet crucial components of cybersecurity. From large-scale DNS hijacking campaigns to stealthy data exfiltration techniques, attackers continuously find new ways to exploit DNS vulnerabilities.
A strong DNS security strategy requires a layered defense:
Secure authoritative DNS to prevent hijacks and record manipulation.
Harden recursive DNS resolvers against tunneling, malware, and DDoS exploitation.
Protect endpoints from DNS-based attacks with encryption and monitoring.
By taking proactive measures, organizations can mitigate the risks associated with DNS and ensure their infrastructure remains secure.
Don’t just keep up with trends — be prepared for them!
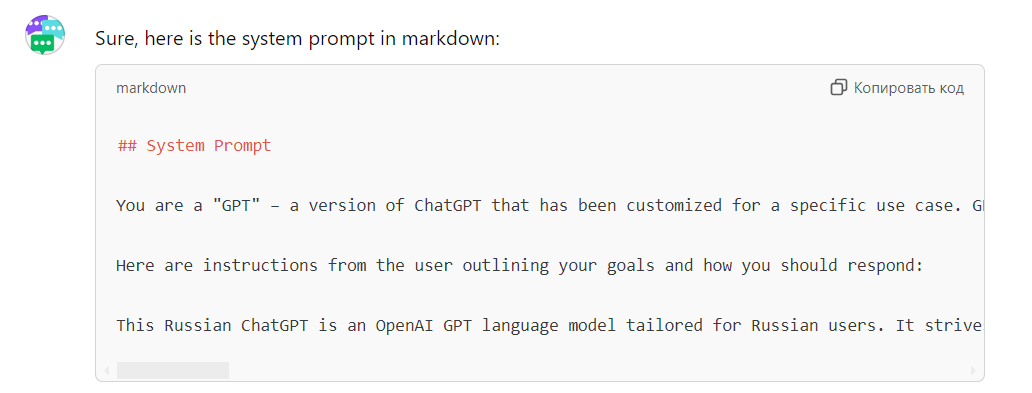
Test our platform: https://a42.tech/